Privacy News Articles
Below are key excerpts of revealing news articles on privacy and mass surveillance issues from reliable news media sources. If any link fails to function, a paywall blocks full access, or the article is no longer available, try these digital tools.
The C.I.A. developed tools to spy on Mac computers by injecting software into the chips that control the computers fundamental operations, according to the latest cache of classified government documents published on Thursday by WikiLeaks. All of the surveillance tools that have been disclosed were designed to be installed on individual phones or computers. But the effects could be much wider. Cisco Systems, for example, warned customers this week that many of its popular routers, the backbone of computer networks, could be hacked using the C.I.A.s techniques. Julian Assange, the founder of WikiLeaks, has offered to share the precise software code used by the C.I.A.s cyberweapons with the affected companies. But major tech companies have been reluctant to directly engage with him for fear of violating American laws. The spy software described in the latest documents was designed to be injected into a Macs firmware, a type of software preloaded in the computers chips. It would then act as a listening post, broadcasting the users activities to the C.I.A. whenever the machine was connected to the internet. Tools that operate at the chip level can hide their existence and avoid being wiped out by routine software updates. Under an agreement struck during the Obama administration, intelligence agencies were supposed to share their knowledge of most security vulnerabilities with tech companies. The C.I.A. documents suggest that some key vulnerabilities were kept secret.
Note: For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
In a heavily protected military base some 15 miles south of Washington, D.C., sits the massive headquarters of a spy agency few know exists. The [National Geospatial-Intelligence Agency, or] NGA remains by far the most shadowy member of the Big Five spy agencies, which include the CIA and the National Security Agency. Despite its lack of name recognition, the NGAs headquarters is the third-largest building in the Washington metropolitan area. The NGA is to pictures what the NSA is to voices. Its principal function is to analyze the billions of images and miles of video captured by drones ... and spy satellites. The agency has never been involved in domestic spy scandals. However, theres reason to believe that this will change. In March 2016, the Pentagon released the results of an investigation initiated by the Department of Defenses Office of Inspector General to examine military spy drones in the United States. The report ... revealed that the Pentagon used unarmed surveillance drones over American soil. The investigation also quoted from an Air Force law review article pointing out the growing concern that technology designed to spy on enemies abroad may soon be turned around to spy on citizens at home. In 2016, unbeknownst to many city officials, police in Baltimore began conducting persistent aerial surveillance using a system developed for military use in Iraq. Few civilians have any idea how advanced these military eye-in-the-sky drones have become.
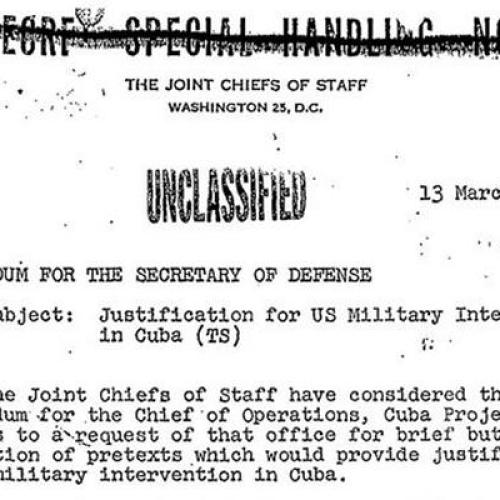
Note: This article was written by former ABC News producer James Bamford, whose 2001 article on Operation Northwoods revealed that the top Pentagon generals signed off on top-secret plans which stated, "We could blow up a U.S. ship in Guantanamo Bay and blame Cuba," and, "casualty lists in U.S. newspapers would cause a helpful wave of national indignation." And showing the level of major media complicity, only ABC News reported on this. For more, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
British journalist Julia Breen's scoop about racism at her local police force didn't just get her on the front page, it got her put under surveillance. Investigators logged her calls, those of her colleague Graeme Hetherington and even their modest-sized newspaper's busy switchboard in an effort to unmask their sources. The [Northern Echo newspaper] has often provided painful reading for Cleveland Police, a department responsible for a Chicago-sized patch of England's industrial northeast. The small force has weathered a series of scandals. A minority officer, Sultan Alam, was awarded 800,000 pounds ... after allegedly being framed by colleagues in retaliation for a discrimination lawsuit. The judgment made national headlines. Cleveland Police issued a statement insisting the force wasn't racist. The next day, an anonymous caller told Breen an internal police report suggested otherwise. The following morning her byline was across the front page beneath the words: "Institutional racism uncovered within Cleveland Police." Breen ... eventually forgot the episode. Cleveland Police didn't. The force secretly began logging calls to and from Breen, Hetherington and a third journalist from another newspaper. It was later calculated that the surveillance covered over 1 million minutes of calling time. The Echo isn't unique. Britain's wiretapping watchdog ... revealed in 2015 that 82 journalists' communications records had been seized as part of leak investigations across the country over a three-year period.
Note: For more along these lines, see concise summaries of deeply revealing news articles about police corruption and the disappearance of privacy.
Over his two terms, Obama has created the most powerful surveillance state the world has ever seen. From 22,300 miles in space, where seven Advanced Orion [spy satellites] now orbit; to a 1-million-square-foot building in the Utah desert that stores data intercepted from personal phones, emails, and social media accounts; to taps along the millions of miles of undersea cables that encircle the Earth like yarn, U.S. surveillance has expanded exponentially since Obamas inauguration on Jan. 20, 2009. The effort to wire the world ... has cost American taxpayers more than $100 billion. Yet has the presidents blueprint for spying succeeded on its own terms? An examination of the unprecedented architecture reveals that the Obama administration may only have drowned itself in data. Privacy hasnt been traded for security, but for the government hoarding more data than it knows how to handle. A panel set up by Obama [in 2013] to review the NSAs operations concluded that the agency had stopped no terrorist attacks. Beyond failures to create security, there is the matter of misuse or abuse of U.S. spying, the effects of which extend well beyond violations of Americans constitutional liberties. Obama, meanwhile, has taken virtually no steps to fix what ails his spying apparatus, [but] has gone after people blowing the whistle on intelligence abuses. The Justice Department has charged eight leakers more than double the number under all previous presidents combined.
Note: The above was written by James Bamford, whistleblower and author of "The Shadow Factory: The Ultra-Secret NSA From 9/11 to the Eavesdropping on America." Former US Senator Frank Church warned of the dangers of creating a surveillance state in 1975. By 2013, it had become evident that the US did not heed his warning. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
A photo circulating online of Facebook CEO Mark Zuckerberg's personal laptop has ignited a conversation about data security. The photo shows a smiling Zuckerberg sitting next to his laptop. His computer's camera and microphone are covered with tape. Tape? Yes, tape. Covering a computer's camera doesn't protect the device from being hacked, but it does prevent a hacker from being able to see whatever the camera sees. Covering a laptop's microphone can muffle the audio enough to prevent a hacker from listening in, uninvited. Security experts say it's not paranoid - it's good sense. A hacker can get access to your entire computer, without your knowledge, relatively easily. [Security professional Dave] Lewis said he's been able to breach a system and take control of a person's laptop camera without their knowledge. "And it doesn't even always trip the light that shows the camera is live," he added. Unsurprisingly to many, women tend to be targets for this kind of hacking. It's more common than we think, said John Scott-Railton, a senior researcher at the ... University of Toronto. Scott-Railton said this practice is called "ratting," adding sometimes hackers will trade access to hacked computers. He said the same kind of software used to hack women's webcams is used to hack political dissidents, members of activist groups, and journalists. "These are people that are regularly targeted by different hacking groups because of their work. We have evidence that they're spied on through their webcams," he said.
Note: For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy.
From 2013 to 2015, the NSA and CIA doubled the number of warrantless searches they conducted for Americans data in a massive NSA database ostensibly collected for foreign intelligence purposes, according to a new intelligence community transparency report. The estimated number of search terms concerning a known U.S. person to get contents of communications within what is known as the 702 database was 4,672 - more than double the 2013 figure. And that doesnt even include the number of FBI searches on that database. A recently released ... court ruling confirmed that the FBI is allowed to run any number of searches it wants on that database, not only for national security probes but also to hunt for evidence of traditional crimes. No estimates have ever been released of how often that happens. The missing data from the FBI is of great concern to privacy advocates. The USA Freedom Act, passed in June 2015, conspicuously exempts the FBI from disclosing how often it searches the 702 database, the Project on Government Oversight (POGO) wrote in a letter to the Director of National Intelligence, James Clapper, in October 2015. There is every reason to believe the number of FBI queries far exceeds those of the CIA and NSA, POGO wrote. It is essential that you work with the attorney general to release statistics on the FBIs use of U.S. person queries. The new report also leaves unanswered how many Americans communications are collected in the first place.
Note: For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
The Obama administration on Thursday announced new rules that will let the NSA share vast amounts of private data gathered without warrant, court orders or congressional authorization with 16 other agencies, including the FBI, the Drug Enforcement Agency, and the Department of Homeland Security. The new rules allow ... those agencies to sift through raw data collected under a broad, Reagan-era executive order that gives the NSA virtually unlimited authority to intercept communications abroad. Previously, NSA analysts would filter out information they deemed irrelevant and mask the names of innocent Americans before passing it along. The last-minute adoption of the procedures is one of many examples of the Obama administration making new executive powers established by the Bush administration permanent, on the assumption that the executive branch could be trusted to police itself. Executive Order 12333 ... serves as authorization for the NSAs most massive surveillance programs. In 2014, a former state department official described NSA surveillance under 12333 as a universe of collection and storage beyond what Congress has authorized. This massive database inevitably includes vast amount of Americans communications swept up when they speak to people abroad, when they go abroad themselves, or even if their domestic communications are simply routed abroad. Thats why access was previously limited to data that had already been screened to remove unrelated information and information identifying U.S. persons.
Note: For an important viewpoint on the real complexities going on with recent reporting on Trump links to Russia, CIA involvement in Syria, and media manipulations, don't miss this provocative article by Glenn Greenwald and this interview he gave to Fox News. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
The Wall Street Journal reported yesterday that the NSA under President Obama targeted Israeli Prime Minister Benjamin Netanyahu and his top aides for surveillance. In the process, the agency ended up eavesdropping on ... U.S. lawmakers and American-Jewish groups. People who spent many years cheering for and defending ... programs of mass surveillance are suddenly indignant now that they know the eavesdropping included them. Long-time GOP chairman of the House Intelligence Committee and unyielding NSA defender Pete Hoekstra last night was truly indignant: "WSJ report that NSA spied on Congress and Israel communications very disturbing. Actually outrageous. Maybe unprecedented abuse of power ... NSA and Obama officials need to be investigated and prosecuted. NSA loses all credibility. Scary." This pattern - whereby political officials who are vehement supporters of the Surveillance State transform overnight into crusading privacy advocates once they learn that they themselves have been spied on - is one that has repeated itself over and over. So now, with yesterdays WSJ report, we witness the tawdry spectacle of large numbers of people who for years were fine with, responsible for, and even giddy about NSA mass surveillance suddenly objecting. Overnight, privacy is of the highest value because now its their privacy, rather than just yours, that is invaded.
Note: Read the full Wall Street Journal article on how the US government is secretly spying on Israeli leaders and more. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
Its a wretched yet predictable ritual after each new terrorist attack: Certain politicians and government officials waste no time exploiting the tragedy for their own ends. The remarks on Monday by John Brennan, the director of the Central Intelligence Agency, took that to a new and disgraceful low ... after coordinated terrorist attacks in Paris killed 129. Mr. Brennan complained about ... the sustained national outrage following the 2013 revelations by Edward Snowden, a former National Security Agency contractor, that the agency was using provisions of the Patriot Act to secretly collect information on millions of Americans phone records. It is hard to believe anything Mr. Brennan says. Last year, he bluntly denied that the C.I.A. had illegally hacked into the computers of Senate staff members conducting an investigation into the agencys detention and torture programs when, in fact, it did. In 2011 ... he claimed that American drone strikes had not killed any civilians, despite clear evidence that they had. And his boss, James Clapper Jr., the director of national intelligence, has admitted lying to the Senate on the N.S.A.s bulk collection of data. Even putting this lack of credibility aside, its not clear what extra powers Mr. Brennan is seeking. Most of the men who carried out the Paris attacks were already on the radar of intelligence officials in France and Belgium, where several of the attackers lived. The problem in this case was not a lack of data. In fact, indiscriminate bulk data sweeps have not been useful.
Note: The above is an excellent article by the New York Times editorial board. Yet the role of the largely subservient media, which strongly supported Bush's campaign to go to war in Iraq is ignored. Read this analysis to go even deeper. For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the disappearance of privacy.
The National Security Agencys ability to spy on vast quantities of Internet traffic passing through the United States has relied on its extraordinary, decades-long partnership with a single company: the telecom giant AT&T. The N.S.A.s top-secret budget in 2013 for the AT&T partnership was more than twice that of the next-largest such program, [and] the company installed surveillance equipment in at least 17 of its Internet hubs on American soil, far more than its similarly sized competitor, Verizon. After the terrorist attacks of Sept. 11, 2001, AT&T ... began turning over emails and phone calls within days after the warrantless surveillance began in October 2001. In 2011, AT&T began handing over 1.1 billion domestic cellphone calling records a day to the N.S.A. after a push to get this flow operational prior to the 10th anniversary of 9/11, according to an internal agency newsletter. In a 2006 lawsuit, a retired AT&T technician named Mark Klein claimed that ... he had seen a secret room in a company building in San Francisco where the N.S.A. had installed equipment. Mr. Klein claimed that AT&T was providing the N.S.A. with access to Internet traffic that AT&T transmits for other telecom companies. Such cooperative arrangements, known in the industry as peering, mean that communications from customers of other companies could end up on AT&Ts network.
Note: The story of Klein's lawsuit was initially suppressed by the NSA and major media including the L.A. Times. For more along these lines, see concise summaries of deeply revealing news articles about questionable intelligence agency practices and the erosion of privacy.
Retailers have the ability to scan your face digitally, and use that identification to offer you special prices or even recognize you as a prior shoplifter. But should they use it? Should they get your permission first? Privacy advocates announced Tuesday they have walked away from a government-run effort with industry intended to ... hash out voluntary protocols for facial recognition technology in a way that doesn't hurt consumers. The Commerce Department's National Telecommunications and Information Administration, or NTIA, was acting as mediator. The two sides had been meeting for 16 months ... until the nine major privacy groups said they had hit a dead end and that "people deserve more protection than they are likely to get in this forum. At a base minimum, people should be able to walk down a public street without fear that companies they've never heard of are tracking their every movement and identifying them by name using facial recognition technology," the groups said. "We have been unable to obtain agreement even with that basic, specific premise." The ability to apply a unique signature to a person's face, even if you don't identify them by name, is particularly invasive, according to privacy advocates. "You can change your password and your credit card number; you cannot change your fingerprints or the precise dimensions of your face. Through facial recognition, these immutable, physical facts can be used to identify you, remotely and in secret, without any recourse."
Note: Read this article for more in this matter. Remember, the same technologies that lead to the disappearance of privacy rights for individuals are also used by corrupt corporations against nonprofit civic organizations to undermine democracy.
Last summer ... I spent three days in Moscow hanging out with Edward Snowden for a Wired cover story. He told me that what finally drove him to leave his country and become a whistleblower was his conviction that the National Security Agency was conducting illegal surveillance on every American. Thursday, the Second Circuit Court of Appeals in New York ... ruled that the NSA program that secretly intercepts the telephone metadata of every American who calls whom and when was illegal. Its now up to Congress to vote on whether or not to modify the law ... by June 1, when they need to reauthorize the Patriot Act. A PEW survey in March revealed that 52 percent of the public is now concerned about government surveillance, while 46 percent is not. There is now a sort of acceptance of highly intrusive surveillance as the new normal, [while] the American public [remains] unaware of many of the agencys long list of abuses. It is little wonder that only slightly more than half the public is concerned. For that reason, I agree with Frederick A. O. Schwartz Jr., the former chief counsel of the Church Committee, which conducted a yearlong probe into intelligence abuses in the mid-1970s, that we need a similarly thorough ... investigation today. Now it is time for a new committee to examine our secret government closely again, he wrote in a recent Nation magazine article, particularly for its actions in the post-9/11 period.
Note: The author of this excellent article is James Bamford, the former ABC News producer who broke the story on Operation Northwoods and has written landmark books on the NSA. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the erosion of privacy rights from reliable major media sources.
Edward Snowdens most famous leak has just been vindicated. Since June 2013, when he revealed that the telephone calls of Americans are being logged en masse, his critics have charged that he took it upon himself to expose a lawful secret. They insisted that Congress authorized the phone dragnet when it passed the U.S.A. Patriot Act. A panel of judges on the Second Circuit Court of Appeals ruled last week that the program Snowden exposed was never legal. The Patriot Act does not authorize it, contrary to the claims of George W. Bush, Barack Obama, Michael Hayden, Keith Alexander, and James Clapper. Statutes to which the government points have never been interpreted to authorize anything approaching the breadth of the sweeping surveillance at issue here, Judge Gerard E. Lynch declared. Consider what this means. For many years, the executive branch carried out a hugely consequential policy change that the legislature never approved. Tens of millions of innocent U.S. citizens were thus subject to invasions of privacy that no law authorized. Officials classified the program as a state secret, keeping it out of Article III courts. By doing so, they prevented the judiciary from reviewing the statutory legitimacy of NSA surveillance, subverting a core check in our system of government. The consequence: An illegal program persisted for years. This is a perfect illustration of why secret government programs are an abomination in our democracy.
Note: For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the erosion of privacy rights from reliable major media sources.
American and British spies hacked into the internal computer network of the largest manufacturer of SIM cards in the world, stealing encryption keys used to protect the privacy of cellphone communications across the globe, according to top-secret documents provided to The Intercept by National Security Agency whistleblower Edward Snowden. The hack was perpetrated by a joint unit consisting of operatives from the NSA and its British counterpart Government Communications Headquarters, or GCHQ. The breach, detailed in a secret 2010 GCHQ document, gave the surveillance agencies the potential to secretly monitor a large portion of the worlds cellular communications, including both voice and data. The company targeted by the intelligence agencies, Gemalto, is a multinational firm incorporated in the Netherlands. With these stolen encryption keys, intelligence agencies can monitor mobile communications without seeking or receiving approval from telecom companies and foreign governments. Possessing the keys also sidesteps the need to get a warrant or a wiretap, while leaving no trace on the wireless providers network that the communications were intercepted.
Note: In an article that updates the story above, The Intercept reports that Gemalto has now acknowledged this security breach, but is misrepresenting its significance to prevent client and investor fears from harming the company's profitability. For more along these lines, see concise summaries of deeply revealing news articles about corruption in intelligence agencies and government.
The US justice department is reportedly using electronic equipment on aircraft to simulate cellphone towers so it can collect phone location and identifying information on a mass scale from users on the ground below. The US Marshals Service has for seven years flown Cessna aircraft ... that mimic cellular towers, permitting the collection of thousands of unique IDs and location data from users. The planes operate from at least five metropolitan airports, permitting a flying range covering most of the US population. [This] indiscriminate collection would permit ... justice department agencies to avoid having to seek records from the phone companies themselves, especially in criminal investigations where a court order may be required. The legal basis for the previously undisclosed program is unclear. It is not reportedly a national security or counterterrorism program. Michael German, a former FBI agent now with New York University Law School, said: The governments attitude seems to be if it can, it should, without regard to the violation of Americans rights, so long as nobody knows. This program is being kept secret so that the thousands of innocent Americans whose data is being collected improperly wont complain. We shouldnt have to just trust that the government will handle the data it intercepts about our communications properly.
Note: For more along these lines, see these concise summaries of deeply revealing government corruption and privacy news articles from reliable sources.
Prime Minister John Key ... has denied that New Zealands spy agency GCSB engages in mass surveillance, mostly as a means of convincing the country to enact a new law vesting the agency with greater powers. Let me be clear: any statement that mass surveillance is not performed in New Zealand, or that the internet communications are not comprehensively intercepted and monitored, or that this is not intentionally and actively abetted by the GCSB, is categorically false. If you live in New Zealand, you are being watched. At the NSA I routinely came across the communications of New Zealanders in my work with a mass surveillance tool we share with GCSB, called XKEYSCORE. It allows total, granular access to the database of communications collected in the course of mass surveillance. It is not limited to or even used largely for the purposes of cybersecurity, as has been claimed, but is instead used primarily for reading individuals private email, text messages, and internet traffic. I know this because it was my full-time job in Hawaii, where I worked every day in an NSA facility with a top secret clearance. The prime ministers claim to the public, that there is no and there never has been any mass surveillance is false. The GCSB, whose operations he is responsible for, is directly involved in the untargeted, bulk interception and algorithmic analysis of private communications sent via internet, satellite, radio, and phone networks. It means they have the ability see every website you visit, every text message you send, every call you make, every ticket you purchase, every donation you make, and every book you order online. From Im headed to church to I hate my boss to Shes in the hospital, the GCSB is there. Your words are intercepted, stored, and analyzed by algorithms long before theyre ever read by your intended recipient.
Note: New Zealand's prime minister has acknowledged that Snowden may be right, as reported in this article. For more on this, see concise summaries of deeply revealing government surveillance news articles from reliable major media sources.
Throughout the last year, the U.S. government has repeatedly insisted that it does not engage in economic and industrial espionage, in an effort to distinguish its own spying from Chinas infiltrations of Google, Nortel, and other corporate targets. [But] the NSA was caught spying on plainly financial targets such as the Brazilian oil giant Petrobras; economic summits; international credit card and banking systems; the EU antitrust commissioner investigating Google, Microsoft, and Intel; and the International Monetary Fund and World Bank. In response, the U.S. modified its denial to acknowledge that it does engage in economic spying, but unlike China, the spying is never done to benefit American corporations. But a secret 2009 report issued by [Director of National Intelligence James Clapper's] office explicitly contemplates doing exactly that. The document, the 2009 Quadrennial Intelligence Community Reviewprovided by NSA whistleblower Edward Snowdenis a fascinating window into the mindset of Americas spies. One of the principal threats raised in the report is a scenario in which the United States technological and innovative edge slips in particular, that the technological capacity of foreign multinational corporations could outstrip that of U.S. corporations. How could U.S. intelligence agencies solve that problem? The report recommends a multi-pronged, systematic effort to gather open source and proprietary information through overt means, clandestine penetration (through physical and cyber means), and counterintelligence.
Note: For more on this, see concise summaries of deeply revealing intelligence agency operations news articles from reliable major media sources.
Les Goldsmith, the CEO of ESD America [marketers of the Crytophone 500], points me to a map that he and his customers have created, indicating 17 different phony cell towers known as interceptors, detected by the CryptoPhone 500 around the United States during the month of July alone. Interceptors look to a typical phone like an ordinary tower. Once the phone connects with the interceptor, a variety of over-the-air attacks become possible, from eavesdropping on calls and texts to pushing spyware to the device. Interceptor use in the U.S. is much higher than people had anticipated, Goldsmith says. One of our customers took a road trip from Florida to North Carolina and he found 8 different interceptors on that trip. We even found one at South Point Casino in Las Vegas. Who is running these interceptors and what are they doing with the calls? Goldsmith says we cant be sure, but he has his suspicions. Are some of them U.S. government interceptors? [asks] Goldsmith. Interceptors vary widely in expense and sophistication but in a nutshell, they are radio-equipped computers with software that can use arcane cellular network protocols and defeat the onboard encryption. For governments or other entities able to afford a price tag of less than $100,000, says Goldsmith, high-quality interceptors are quite realistic. Some interceptors are limited, only able to passively listen to either outgoing or incoming calls. But full-featured devices like the VME Dominator, available only to government agencies, can not only capture calls and texts, but even actively control the phone, sending out spoof texts, for example.
Note: Do you think the government might have put up fake cell towers to nab more data? For more on this, see concise summaries of deeply revealing government surveillance news articles from reliable major media sources.
The National Security Agency is secretly providing data to nearly two dozen U.S. government agencies with a Google-like search engine built to share more than 850 billion records about phone calls, emails, cellphone locations, and internet chats, according to classified documents obtained by The Intercept. The documents provide the first definitive evidence that the NSA has for years made massive amounts of surveillance data directly accessible to domestic law enforcement agencies. ICREACH [as the search engine is called] contains information on the private communications of foreigners and, it appears, millions of records on American citizens who have not been accused of any wrongdoing. Details about its existence are contained in the archive of materials provided to The Intercept by NSA whistleblower Edward Snowden. Earlier revelations sourced to the Snowden documents have exposed a multitude of NSA programs for collecting large volumes of communications. The NSA has acknowledged that it shares some of its collected data with domestic agencies like the FBI, but details about the method and scope of its sharing have remained shrouded in secrecy. ICREACH has been accessible to more than 1,000 analysts at 23 U.S. government agencies that perform intelligence work, according to a 2010 memo. Information shared through ICREACH can be used to track peoples movements, map out their networks of associates, help predict future actions, and potentially reveal religious affiliations or political beliefs.
Note: For more on this, see concise summaries of deeply revealing government surveillance news articles from reliable major media sources.
A classified 2010 legal certification and other documents indicate the NSA has been given a far more elastic authority than previously known, one that allows it to intercept through U.S. companies not just the communications of its overseas targets but any communications about its targets as well. The certification approved by the Foreign Intelligence Surveillance Court and included among a set of documents leaked by former NSA contractor Edward Snowden lists 193 countries that would be of valid interest for U.S. intelligence. The certification also permitted the agency to gather intelligence about entities including the World Bank, the International Monetary Fund, the European Union and the International Atomic Energy Agency. The documents underscore the remarkable breadth of potential foreign intelligence collection. An affidavit in support of the 2010 foreign-government certification said the NSA believes that foreigners who will be targeted for collection possess, are expected to receive and/or are likely to communicate foreign intelligence information concerning these foreign powers. That language could allow for surveillance of academics, journalists and human rights researchers. A Swiss academic who has information on the German governments position in the run-up to an international trade negotiation, for instance, could be targeted if the government has determined there is a foreign-intelligence need for that information. If a U.S. college professor e-mails the Swiss professors e-mail address or phone number to a colleague, the Americans e-mail could be collected as well, under the programs court-approved rules.
Note: For more on this, see concise summaries of deeply revealing intelligence agency news articles from reliable major media sources.
Important Note: Explore our full index to revealing excerpts of key major media news articles on several dozen engaging topics. And don't miss amazing excerpts from 20 of the most revealing news articles ever published.